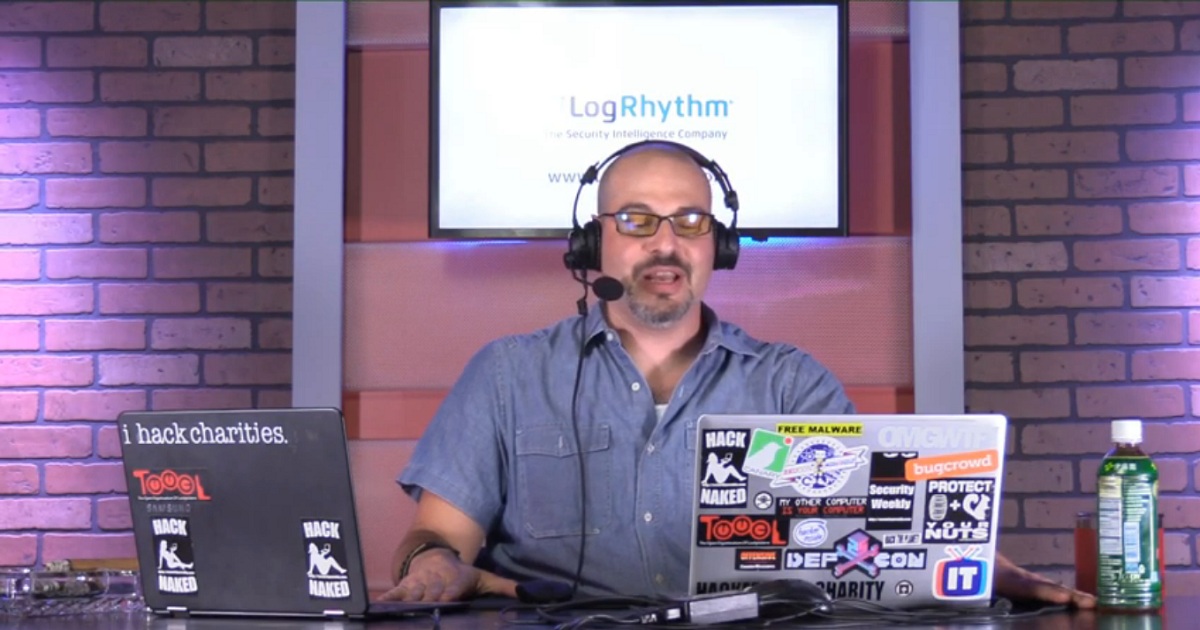
LogRhythm
The MITRE ATT&CK framework is quickly growing in popularity as an effective method to get on the offense of threat detection and response. In this webinar, presenters go beyond definitions and demonstrate how to apply the MITRE ATT&CK framework to your security monitoring. Paul Asadoorian and Matt Alderman of Security Weekly provide an overview of the MITRE ATT&CK framework, discuss how to prioritize the capabilities of the framework, and review some of the existing open source tools for testing/mapping to MITRE.
Watch Now

Did you know that an HAProxy Enterprise load balancer can protect your applications from common threats? In this webinar, we’ll give you an overview of the multilayered security solution provided by HAProxy Enterprise.
Watch Now
NIST
On May 2, 2019, the President issued an Executive Order that recognized America’s cybersecurity workforce as a strategic asset that protects the American people, the homeland, and the American way of life. The executive order further recognized the need to enhance workforce mobility to improve cybersecurity and the importance of supporting the development of cybersecurity skills. This webinar will provide insights into the policy established through this executive order, the tasks and deliverables contained within it, and the consultative process to be used to execute recommendations from the 2017 Report to the President on Supporting the Growth and Sustainment of the Nation’s Cybersecurity Workforce.
Watch Now

Digital transformation and rapid cloud adoption massively impact security postures for organizations of all sizes. The new world of zero perimeters and separation of data storage, compute, and consumption requires a new, holistic approach to access security and provisioning. In their latest Hype Cycle for Data Security 2022, Gartner expands on a new concept—Data Security Governance. Specifically, Data Security Platforms as a modern approach to comprehensive data security and access controls in a world demanding more, faster access to data.
Watch Now