
The only threat more persistent to organizations than cyber criminals? The cyber security skills crisis.
Nearly 60% of enterprises can't find the staff to protect their data (and reputations!) from new and emerging breeds of cyber-attacks, reports the Information Systems Security Association (ISSA) in its 5th annual global industry study.
Watch Now

RedVector
Cyberattacks are the fastest growing crime in the U.S., and they are increasing in size, sophistication and cost. During this webcast, subject matter expert Duane Anderson will: Discuss the major vulnerabilities within cloud-based systems. Explain why it’s critical to keep these systems secure. Provide simple actions (ex. browser settings) that can be taken to protect against hacks.
Watch Now
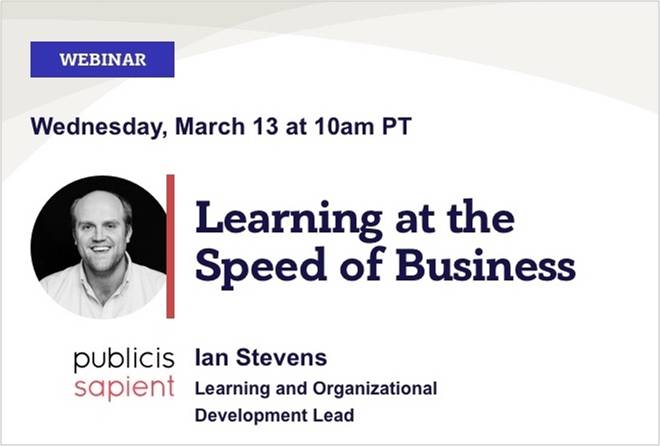
Join Ian Stevens, North America L&D Lead at Publicis Sapient will share his team's successful learning programs that prepared Sapient's consultants to be leaders in digital transformation. Watch now to walk away with: A proven "push-pull" blended learning program How to tie learning with hiring & staffing priorities to motivate
Watch Now

The explosion of edges created by digital acceleration places an enormous strain on any cybersecurity infrastructure. Simply put, security has to be everywhere and traditional security approaches cannot handle today’s challenges.
Watch Now